Today, there are important updates from Ukraine.
Here, the latest Ukrainian covert operation turned into a digital ambush that caught the Russian military completely off guard. What followed became a silent disaster for Russia that left entire sectors paralyzed and scrambling for answers.
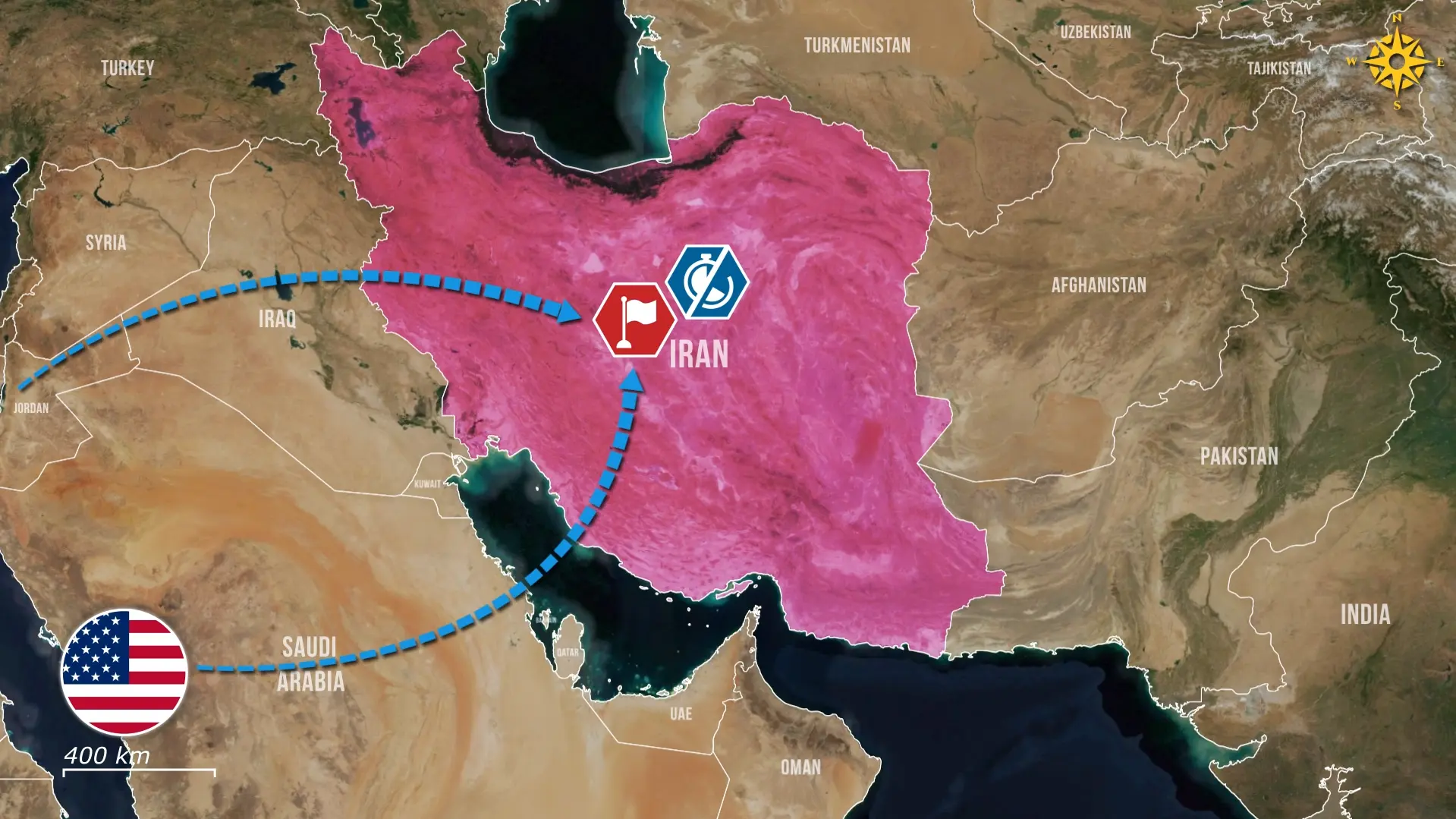
The Ukrainian hacktivist group 256 Cyber Assault Division conducts cyberattacks against the Russian government and military, and now they struck again. The group has just conducted a covert cyber-intelligence operation targeting Russians trying to access Starlink, after they were blocked from using it. They were actively looking for ways to find a workaround, which was exploited by Ukrainian hackers, who anticipated that the Russians would act without precaution to get access again.
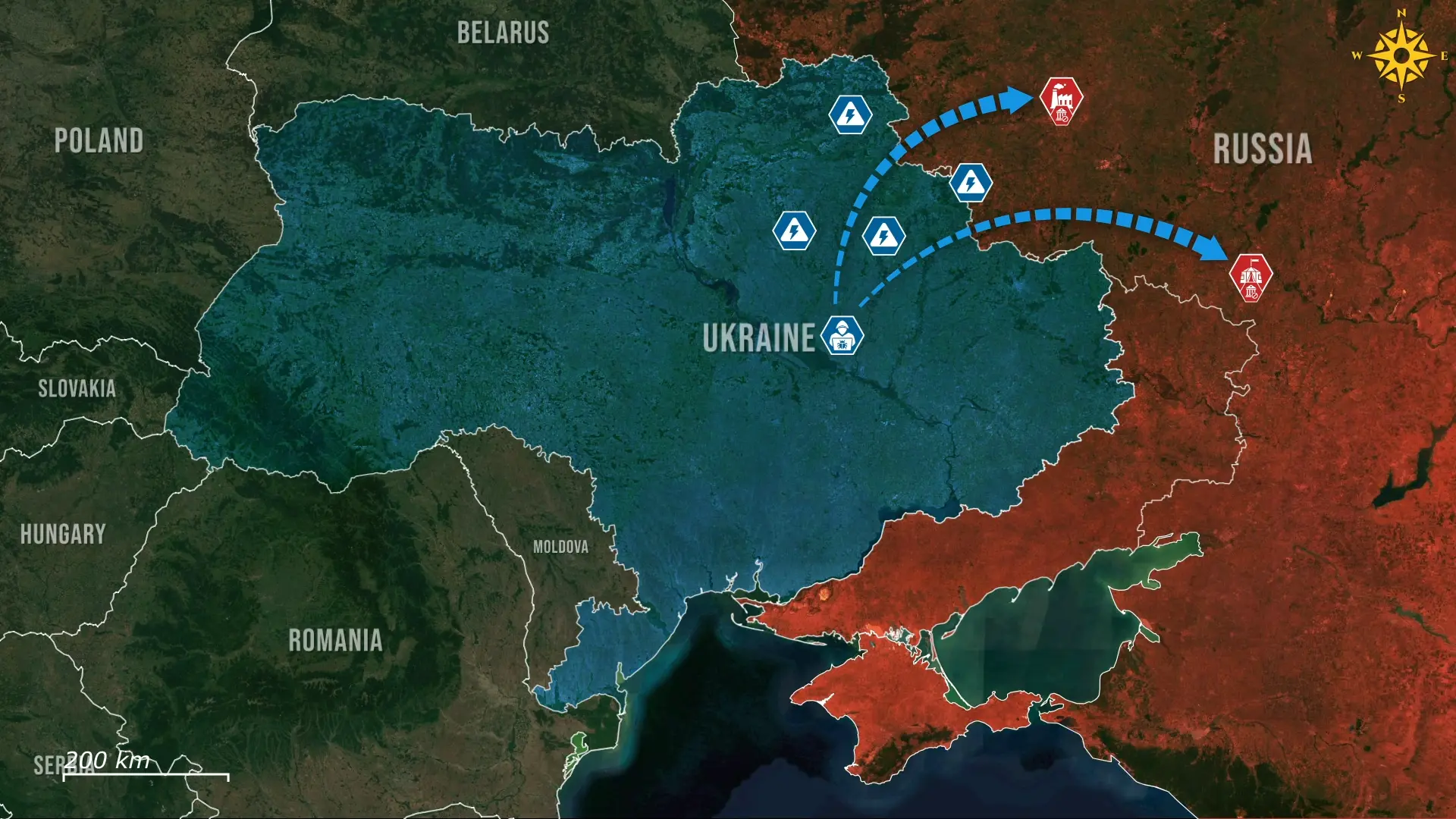
This hacktivist group has now targeted Russian military personnel by exploiting their reliance on Starlink satellite terminals. According to the group, operatives created a network of fake Telegram channels and bots that offered to restore or activate Starlink access either free of charge or for a small fee. Russian soldiers seeking to resolve communication disruptions were allegedly instructed to submit detailed information, including personal data, terminal identifiers, and geolocation coordinates. The organizers claim that within one week, they collected 2,420 data submissions containing precise locations of Russian Starlink terminals and troop positions.

In addition, the group reports receiving 31 inquiries from individuals in Russian-controlled territories who were willing to act as intermediaries to facilitate activation, as well as 5,870 dollars in cryptocurrency payments from Russian personnel attempting to regain connectivity. The collected information, the group states, has been forwarded to Ukrainian authorities for further operational use.

As a result, Ukrainian hackers and data analysts leveraged the collected submissions to identify and map 2,420 Russian Starlink terminals along with their associated positions. These locations included drone operators relying on Starlink connectivity for guidance and remote control, as well as field commanders using the system to maintain battlefield communications and command-and-control functions.
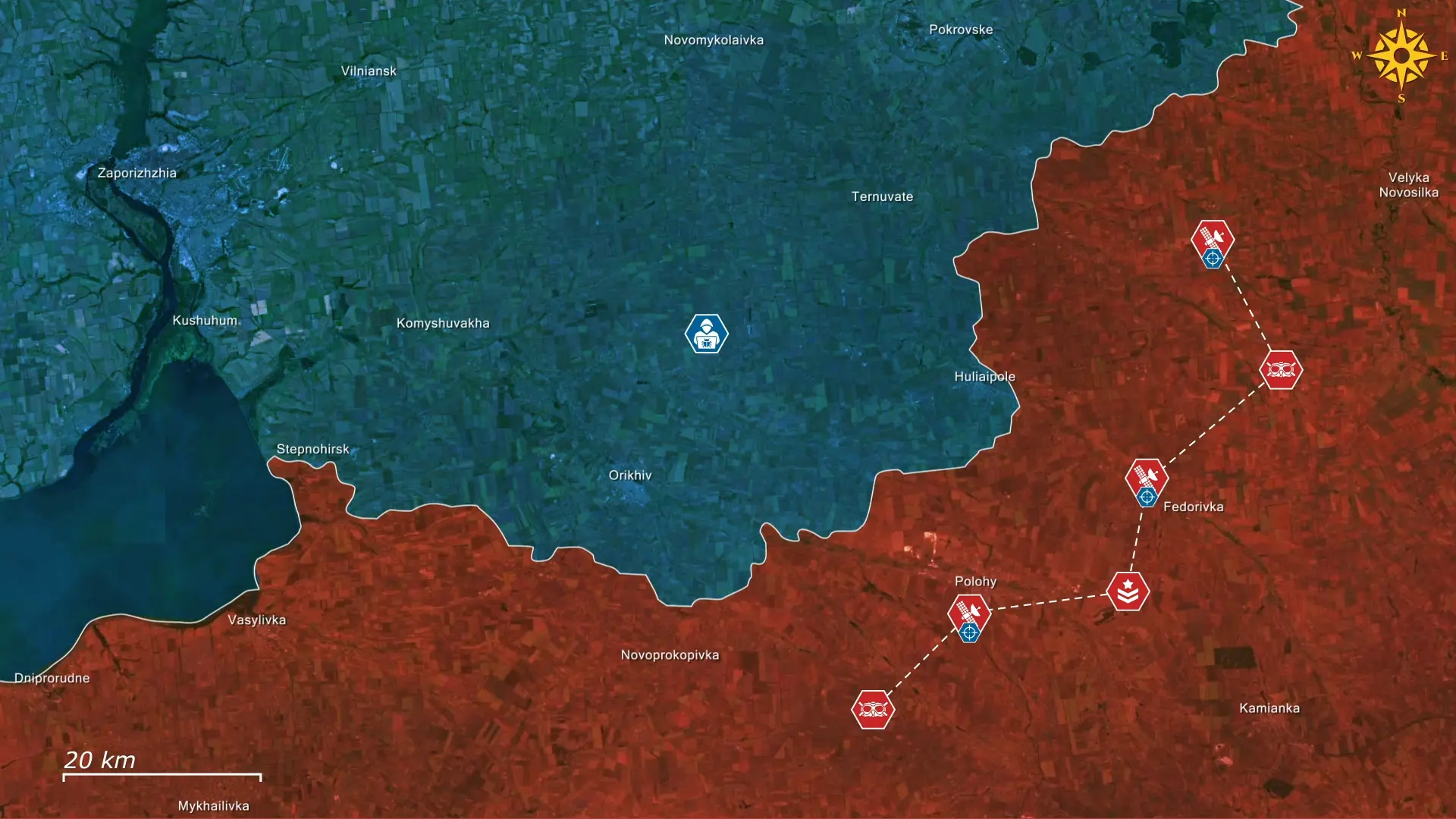
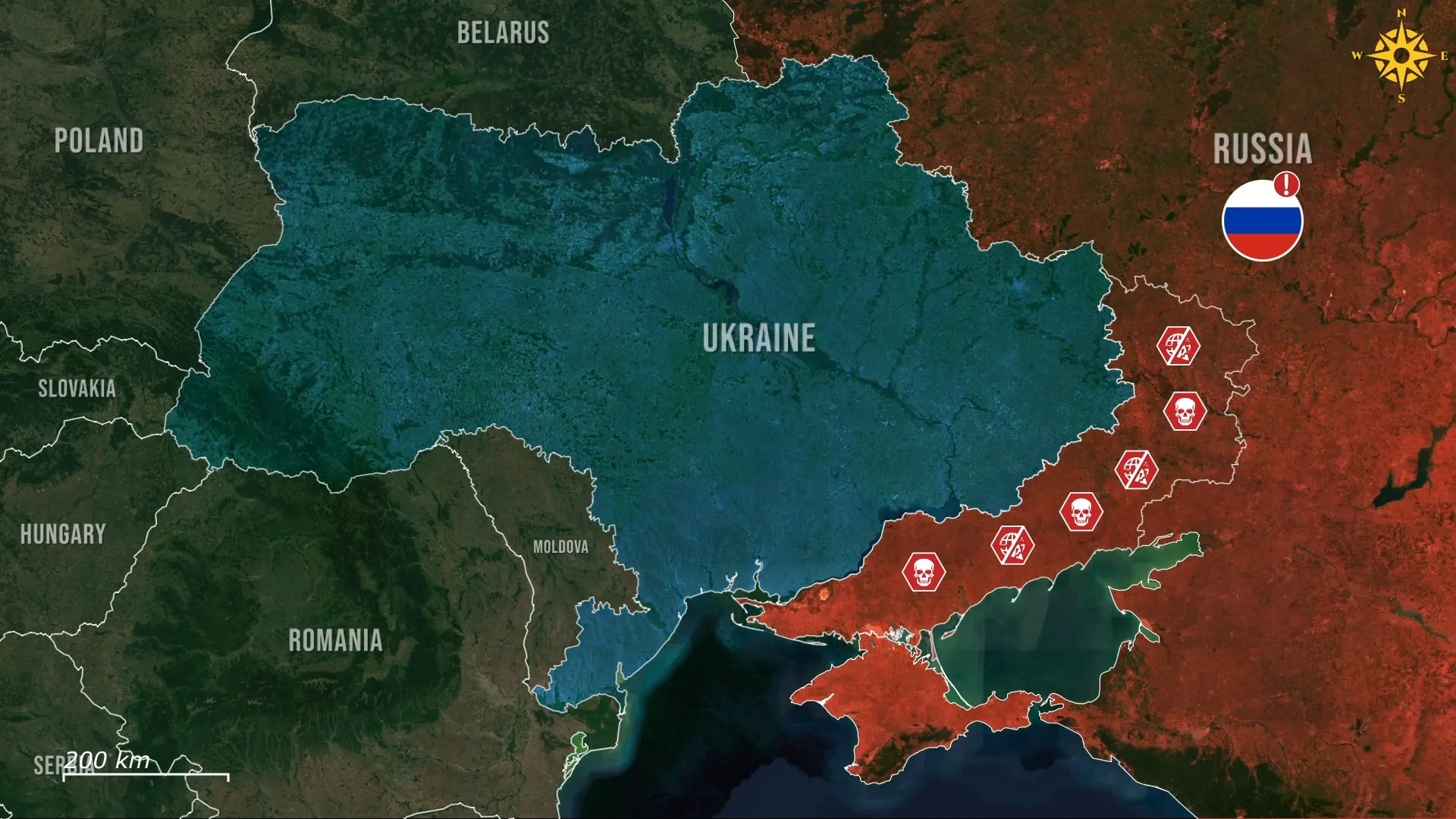
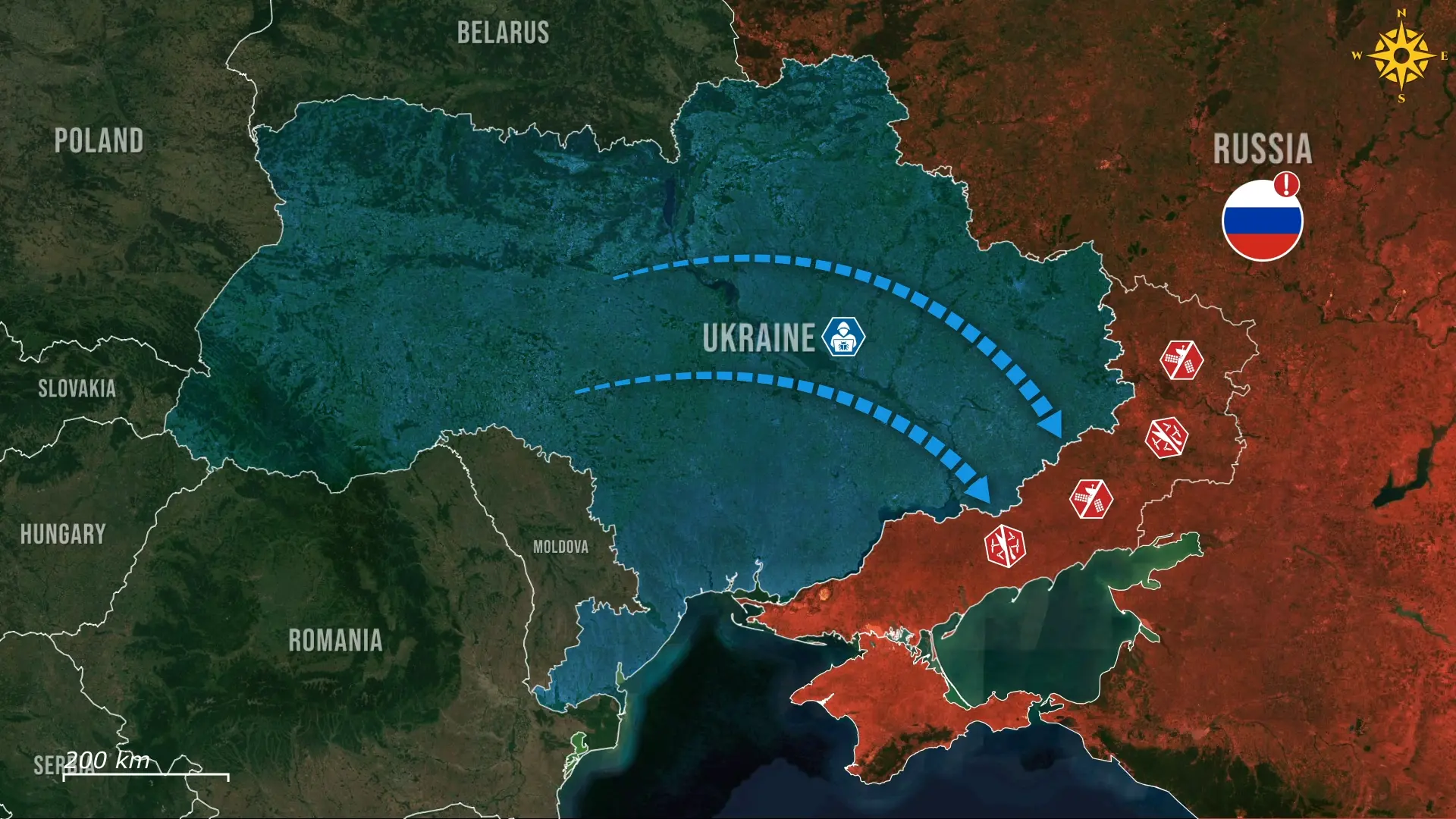
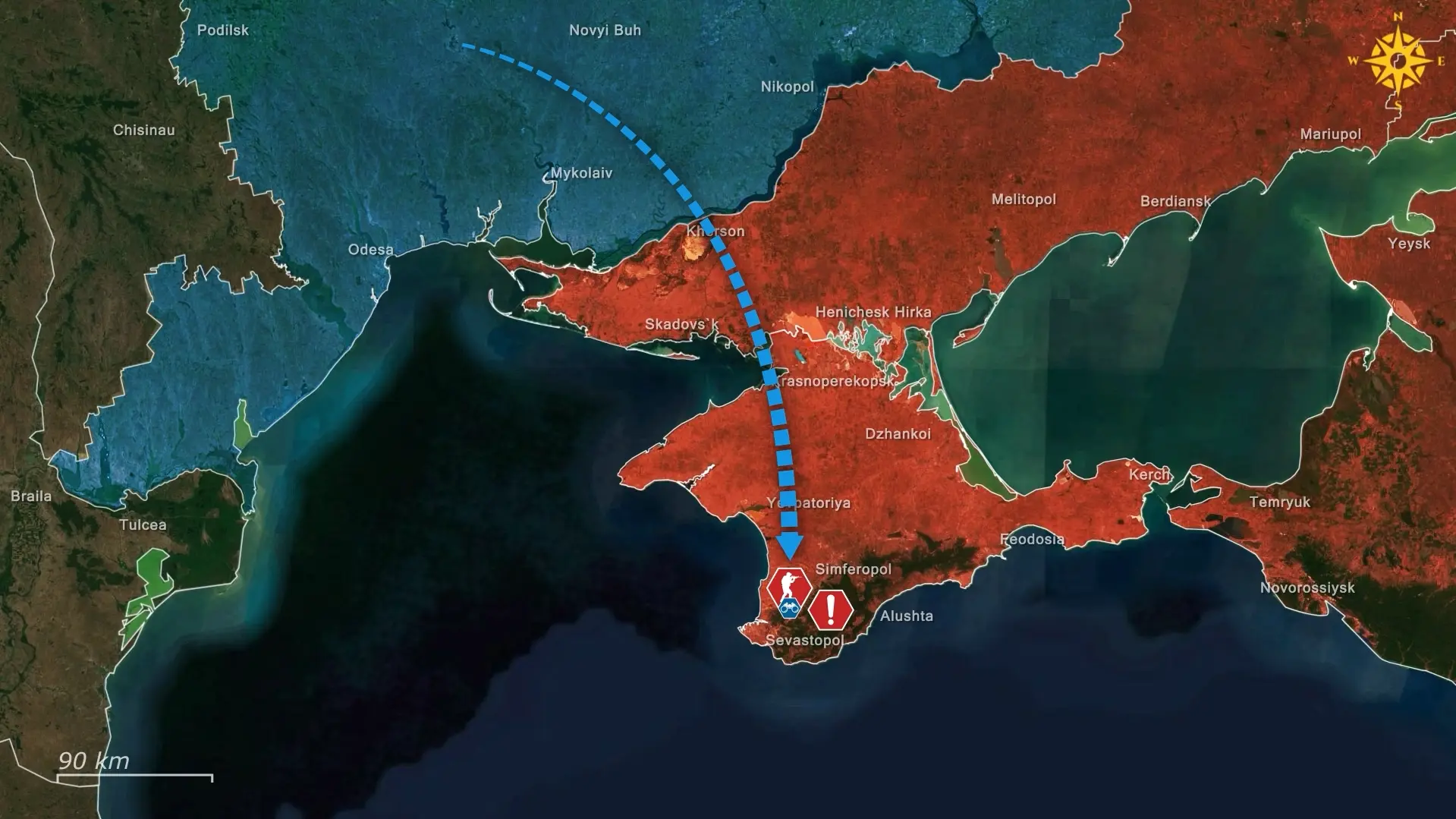
Ukrainian forces acted rapidly on the collected intelligence, exploiting the disclosed geolocation data before Russian units could relocate or recognize that their own submissions had exposed their exact positions to Ukrainian military intelligence. The information was used to coordinate strikes on command centers, drone control hubs, and logistical facilities, reinforcing Ukrainian counteroffensive operations in the Stepnohirsk, Huliaipole, and Dnipropetrovsk sectors.
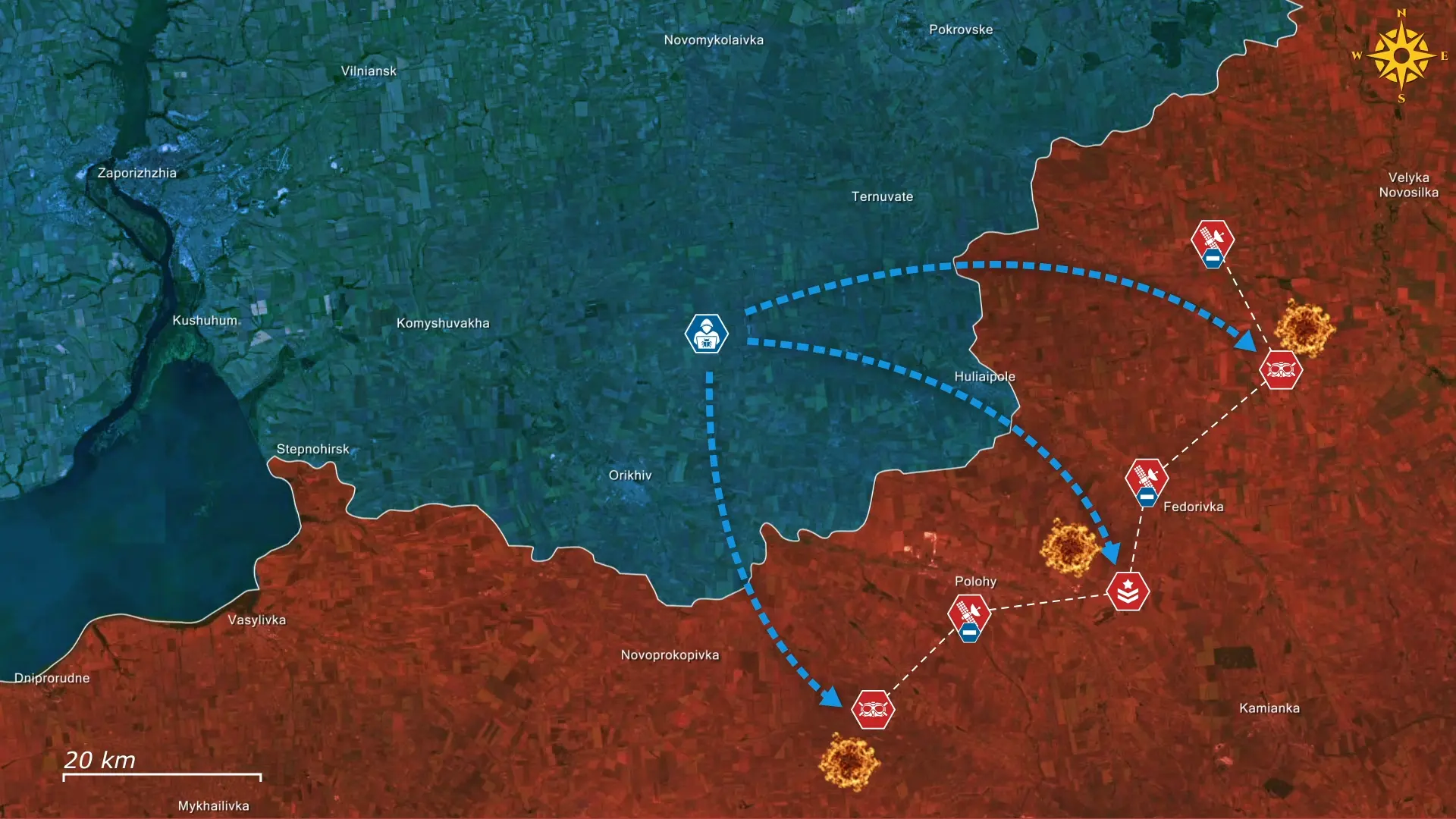
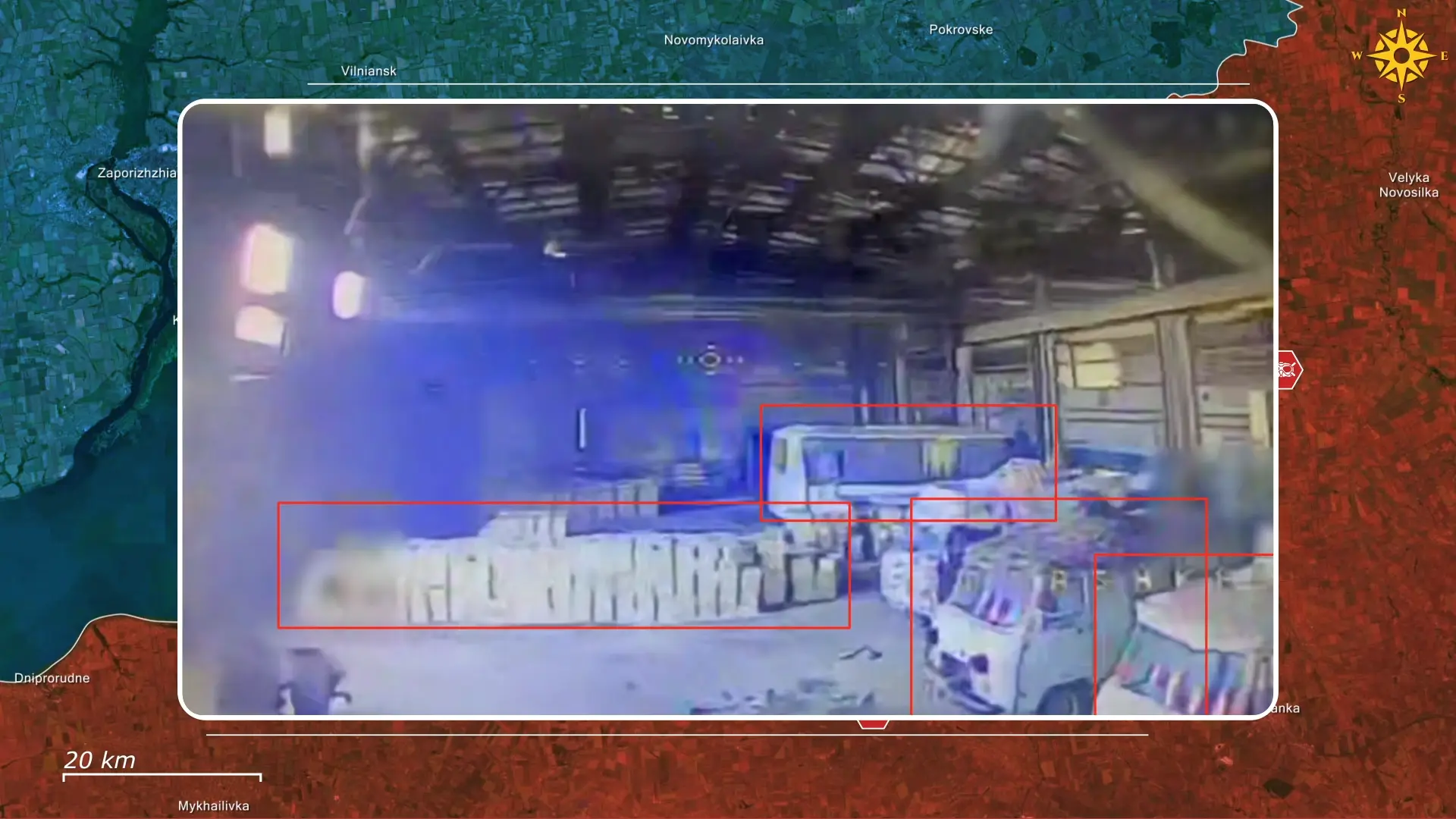
Footage from the area shows a Ukrainian drone striking a Russian warehouse that housed ten vehicles, including vans and a bus, along with approximately 10,000 FPV drones. The strike destroyed the facility, depriving Russian forces in the sector of both transport assets and a significant quantity of precision strike equipment.

Additional video materials indicate that Ukrainian forces prioritized targeting Russian drone operators ahead of broader offensive actions. Among those reportedly killed was Junior Lieutenant Oleksandr Batotsyrenov near Novohryhorivka. He was described as a highly capable FPV drone operator, former special forces member, and artillery platoon commander. His death occurred during Ukrainian preparatory fire preceding offensive operations toward the Oleksandrivka direction.

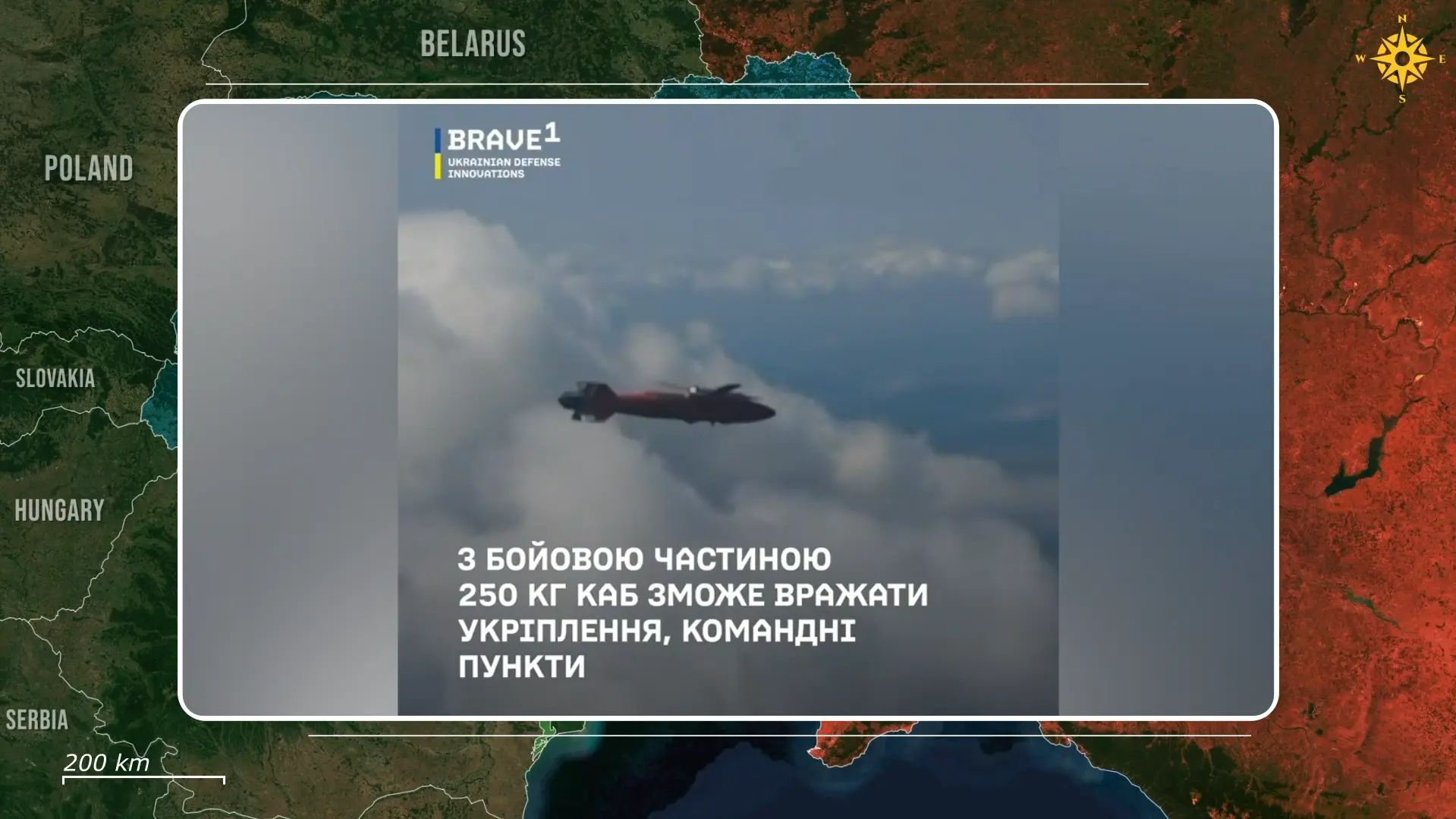
Geolocated footage further shows Ukrainian Mig-29 fighter jets conducting precision strikes against enemy UAV launch sites using AASM Hammer guided bombs. In one strike in Huliaipole, one munition landed near the target while the second achieved a direct hit. In another engagement nearby, one bomb reportedly penetrated the roof of a structure without detonating, while the second struck successfully.
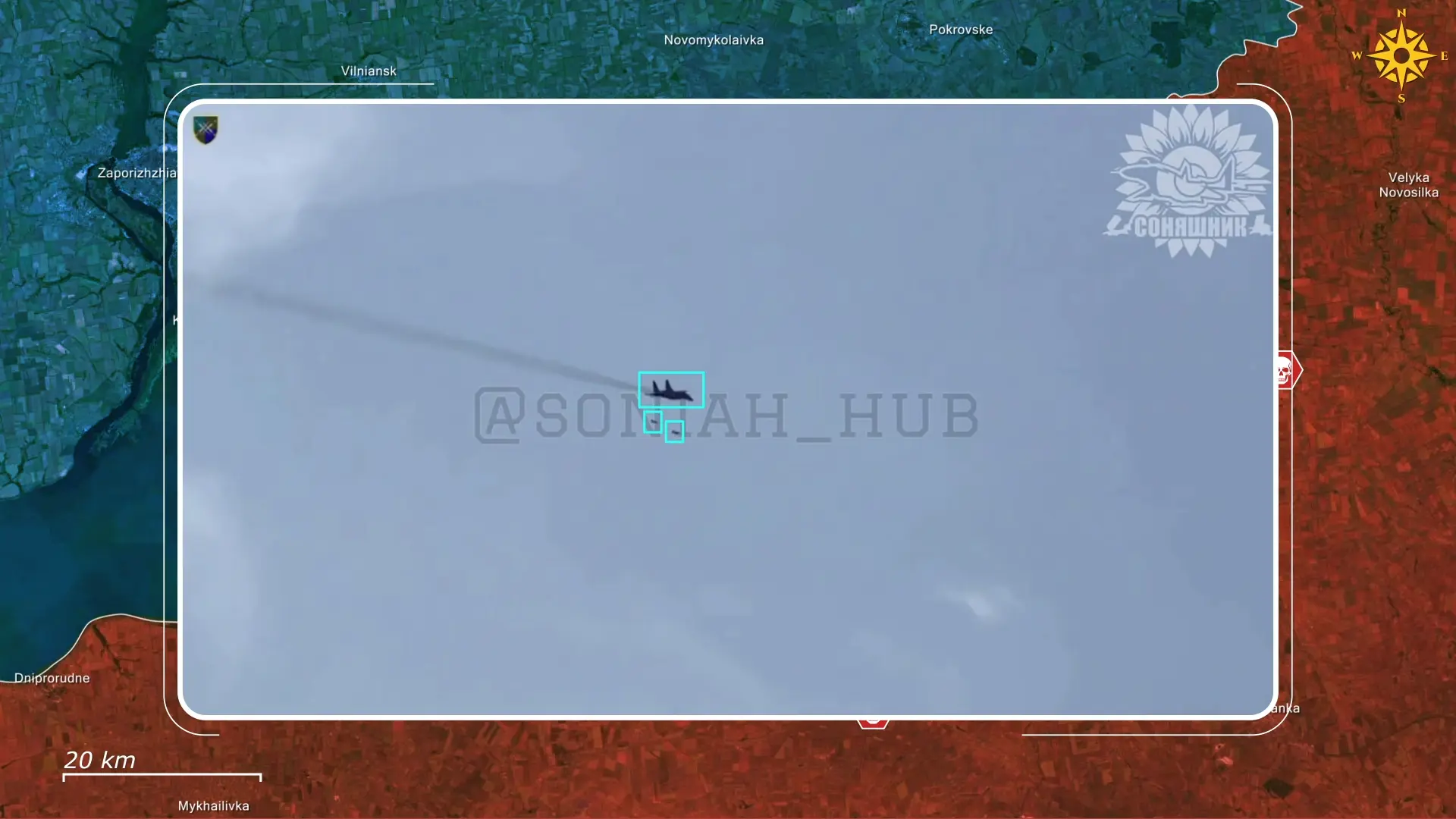

Separate geolocated footage also shows a Ukrainian Mig-29 targeting a bridge in Vasylivka with AASM Hammer bombs. The bridge, recently restored by Russian forces, had been used to support logistics toward Stepnohirsk.


With Starlink already disabled for Russian forces, the situation deteriorated further when Ukrainian strikes eliminated the very operators and command nodes dependent on the system. Drone crews, UAV launch sites, and logistical routes were destroyed, compounding the communications blackout and severely degrading battlefield control, reconnaissance capabilities, and logistical coordination across affected sectors.

These preparatory strikes are not just reducing Russia’s offensive capabilities but also decreasing their effectiveness in defense. Notably, Ukrainian forces are now conducting counterattacks north of Huliaipole, which was facilitated by these strikes, which deprived the Russians of logistics, drones, and drone operators.

Overall, the cyber-intelligence operation and subsequent strikes have compounded the impact of Starlink disruptions, transforming a communications setback into a broader operational crisis for Russian forces. By exposing terminal locations and eliminating their users, Ukrainian forces have significantly degraded battlefield coordination and precision-strike capacity in key sectors before counterattacks. Additional strikes are likely as analysts continue exploiting the harvested geolocation data, targeting remaining terminals and logistics routes. With Russian units scrambling to restore connectivity or find alternatives, their command structure faces mounting paralysis and sustained vulnerability to Ukrainian drone and airstrikes.


.jpg)




Comments